ICFP2007の続き。4405829ページ、”Fuun security features”を見てみる:
なんか暗号化されている。Caesar暗号だと踏んで、文字をシフトするツール
#!ruby |
を作って調べたところ、13ずらした文字が英文になるっぽい。
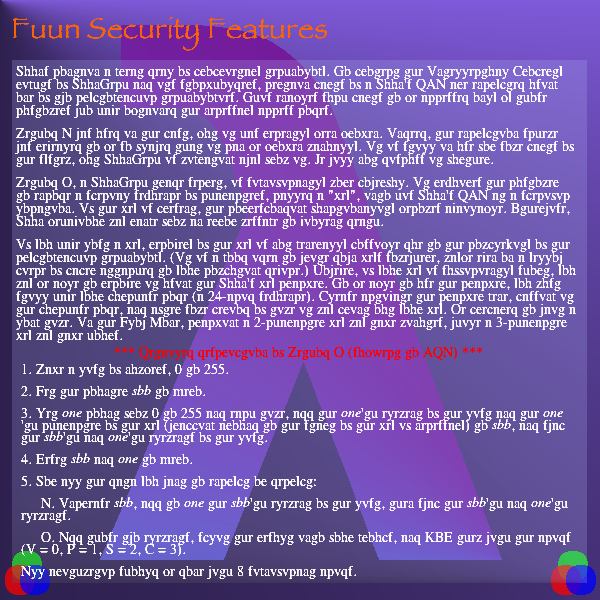
Fuuns contain a great deal of proprietary technology. To protect the Intellectual Property rights of FuunTech and its stockholders, certain parts of a Fuuns DNA are encrypted using customers who have obtained the necessary access codes.
Method A was used in the past, but it has recently been broken. Indeed, the encryption scheme was revealed to be so flawed that it can be broken manually. It is still in use for some parts of the system, but FuunTech is migrating away from it. We will not discuss it further.
Method B, a FuunTech trade secret, is significantly more powerful. It requires the customer to encode a special sequence of characters, called a "key", into his Fuun's DNA at a specific location. If the key is present, the corresponding functionality becomes available. Otherwise, Fuun behaviour may range from an error message to violent death.
If you have lost a key, recovery of the key is not generally possible due to the complexity of the cryptographic technology. (It is a good idea to write down keys somewhere, maybe even on a yellow piece of paper attached to your computing device.) However, if your key is sufficiently short, you may be able to recover it using the Fuun's key cracker. To be able to use the cracker, you must still have your purchase code (a 24-acid sequence). Please activate the cracker gene, passing it the puchase code, and after some period of time it may print out your key. Be prepared to wait a long time. In the Slow Zone, cracking a 2-character key may take minutes, while a 3-character key may take hours.
- Make a list of numbers, 0 to 255.
- Set the counter foo to zero.
- Let bar count from 0 to 255 and each time, add the bar'th element of the list and the bar
- Reset foo and bar to zero.
- For all the data you want to encrypt or decrypt:
- A. Increase foo, add to bar the foo'th element of the list, then swap the foo'th and bar'th elements.
- B. Add those two elements, split the result into four groups, and XOR them with the acids (I = 0, C = 1, F = 2, P = 3)
All arithmetic should be done with 8 significant acids.